How do I conduct a cybersecurity risk assessment for a startup?
To conduct a cybersecurity risk assessment for a startup, you should follow these steps:
- Identify and prioritize the assets that need to be protected. This will typically include things like sensitive data, critical systems and infrastructure, and the reputation of the business.
- Understand the potential threats to these assets. This will involve researching common cybersecurity threats and how they can affect your business, as well as conducting a thorough analysis of your own specific environment and potential vulnerabilities.
- Evaluate the current controls and defenses in place. This will involve reviewing your existing security measures and determining how effective they are at protecting your assets against the identified threats.
- Identify gaps and vulnerabilities. This will involve looking for any areas where your current controls and defenses are inadequate or ineffective, and determining what needs to be done to address those gaps.
- Develop a plan to mitigate the identified risks. This will involve prioritizing the risks based on their likelihood and impact, and then implementing a plan to address the most critical ones first. This may include implementing new security controls, training employees on cybersecurity best practices, and conducting regular security assessments to identify and address any new risks.
Overall, conducting a cybersecurity risk assessment is a crucial step for any startup, as it can help identify potential vulnerabilities and develop a plan to protect against them. By taking a proactive approach to cybersecurity, you can help ensure that your business is well-protected against potential threats.
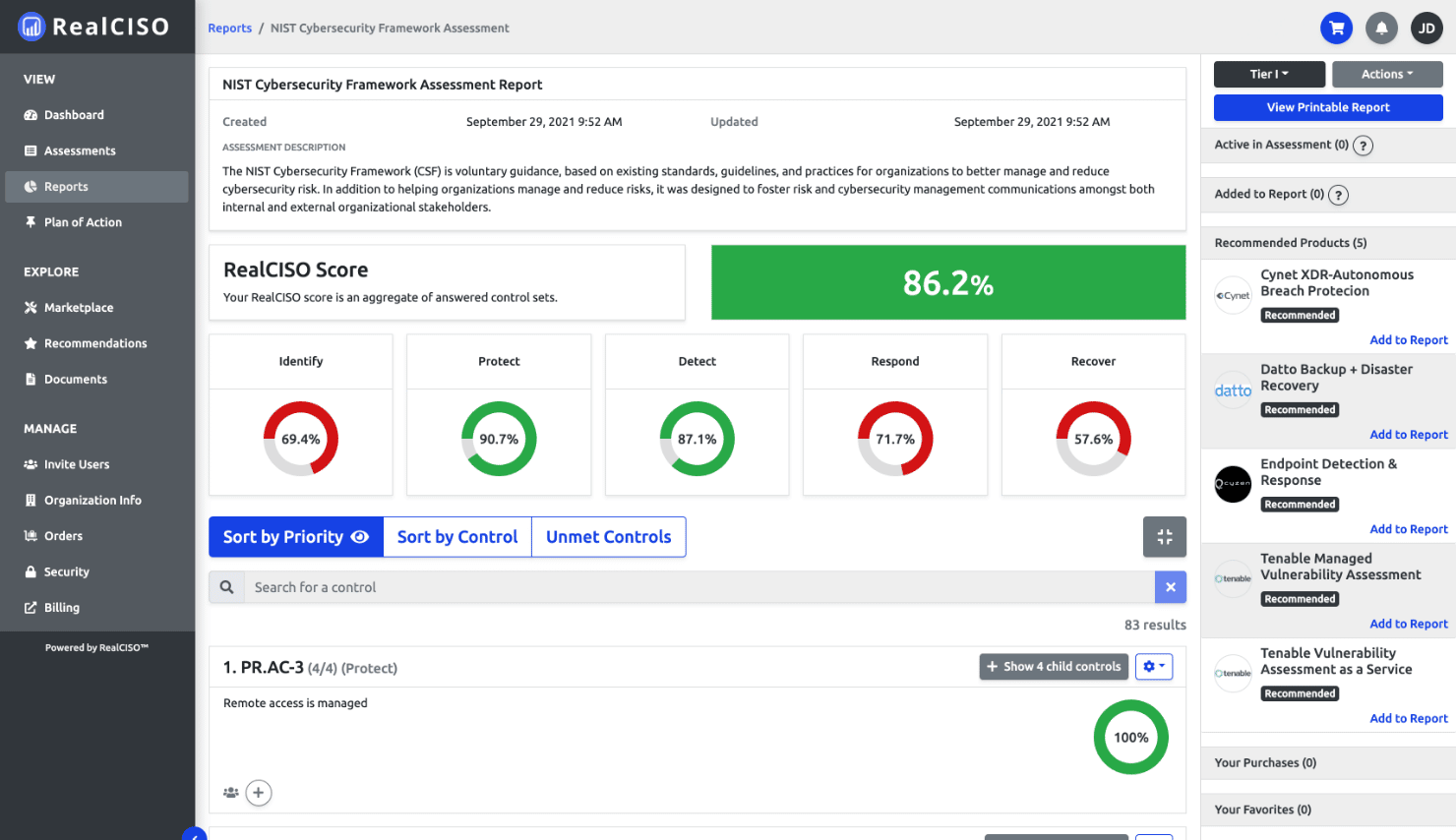
Need a place to start? RealCISO.io can help. Sign up for free to evaluate and improve your organization’s cybersecurity posture to meet compliance with SOC2, CMMC 2.0, NIST 800-171, NIST CSF, HIPAA, and more.