Key Takeaways
- A cybersecurity dashboard is essential for real-time threat monitoring and compliance.
- Effective use requires customization and integration into broader security strategies.
Introduction
A cybersecurity dashboard is vital for tracking and responding to security threats in real time.
Importance of a Cybersecurity Dashboard
In today’s digital landscape, continuous threat monitoring is crucial. A cybersecurity dashboard offers a centralized, real-time view of threats, helping prevent potential breaches and ensuring compliance.
Real-Time Threat Detection
The dashboard’s real-time monitoring allows for immediate detection and response to anomalies, minimizing the risk of breaches and enabling proactive security adjustments.
Cybersecurity Dashboard Compliance Reporting
Dashboards aid in adhering to stringent data security regulations by generating comprehensive reports that support both compliance audits and internal security assessments.
Key Features of a Cybersecurity Dashboard
- Threat Intelligence: Provides real-time and predictive insights for preemptive security.
- Incident Response Management: Features tools for rapid response and recovery after security incidents.
Effectively Using a Cybersecurity Dashboard
Maximize the dashboard’s potential by customizing its features to align with specific organizational needs and integrating it into the overall security strategy.
Conclusion
A well-implemented cybersecurity dashboard enhances an organization’s ability to manage threats and maintain compliance, ultimately strengthening its overall security posture.
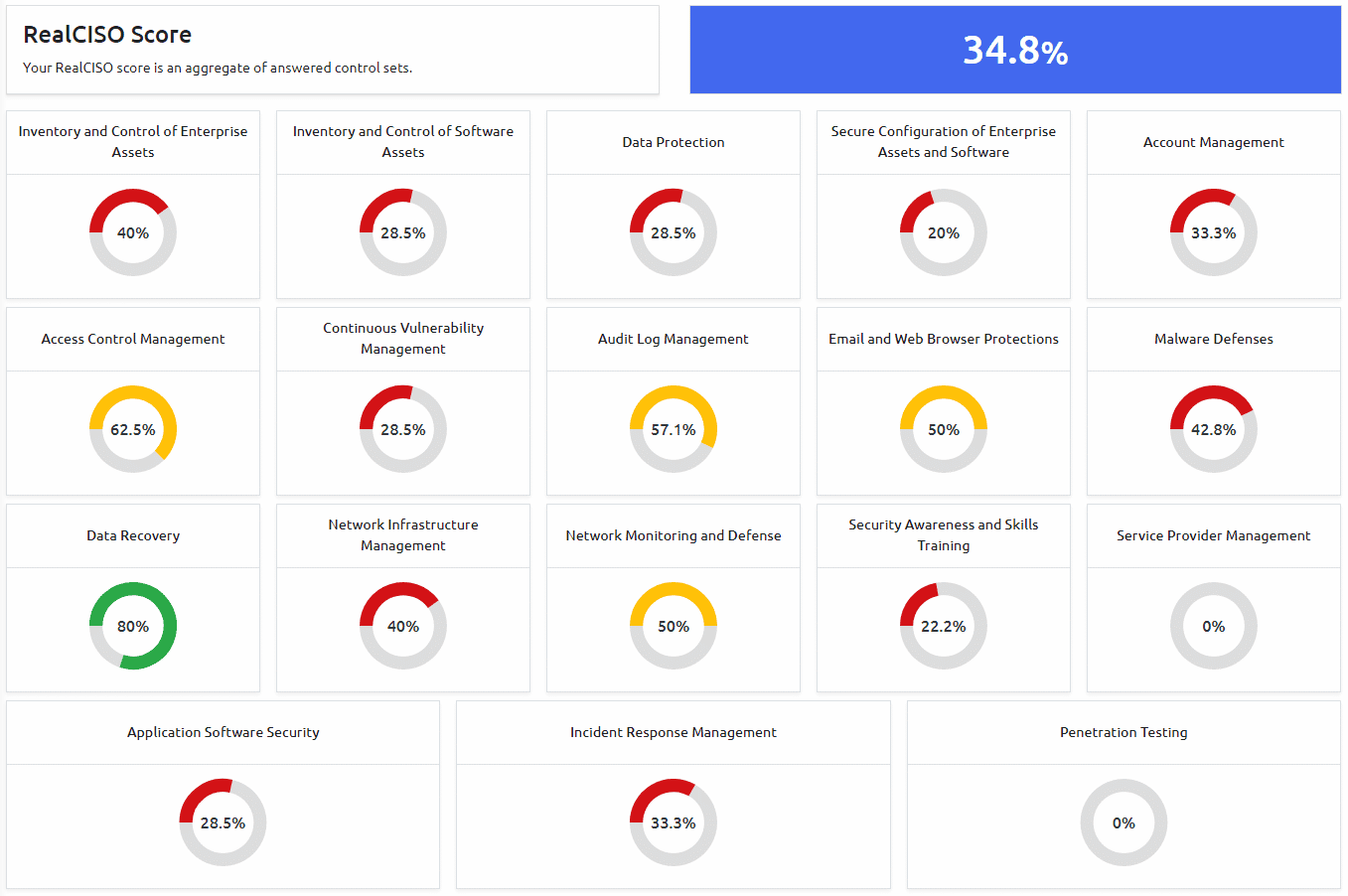
Take Control of Your Cybersecurity Posture with RealCISO
Ready to elevate your organization’s security measures with actionable insights and tailored recommendations? Discover how RealCISO can transform your cybersecurity strategy with just a few clicks. By answering simple questions about your current practices, you’ll receive a clear roadmap to close security gaps and align with industry standards like SOC2, HIPAA, CMMC 2.0, and more. Don’t let the complexity of cyber risk management hold you back.
Learn More about how RealCISO can guide you to a stronger, more resilient security posture.
